
Chinese language menace actors are focusing on ThinkPHP purposes weak to CVE-2018-20062 and CVE-2019-9082 to put in a persistent net shell named Dama.
The online shell permits additional exploitation of the breached endpoints, akin to enlisting them as a part of the attackers’ infrastructure to evade detection in subsequent operations.
The primary indicators of this exercise date again to October 2023, however based on Akamai analysts monitoring it, the malicious exercise has just lately expanded and intensified.
Focusing on previous vulnerabilities
ThinkPHP is an open-source net software growth framework that’s significantly in style in China.
CVE-2018-20062, fastened in December 2018, is a matter found in NoneCMS 1.3, permitting distant attackers to execute arbitrary PHP code by way of crafted use of the filter parameter.
CVE-2019-9082 impacts ThinkPHP 3.2.4 and older, utilized in Open Supply BMS 1.1.1., is a distant command execution downside addressed in February 2019.
The 2 flaws are leveraged on this marketing campaign to allow the attackers to carry out distant code execution, impacting the underlying content material administration methods (CMS) on the goal endpoints.
Particularly, the attackers exploit the bugs to obtain a textual content file named “public.txt,” which, in actuality, is the obfuscated Dama net shell saved as “roeter.php.”
The payload is downloaded from compromised servers positioned in Hong Kong and gives the attackers with distant server management following a easy authentication step utilizing the password “admin.”
Akamai says the servers delivering the payloads are contaminated themselves with the identical net shell, so it seems that compromised methods are changed into nodes within the attacker’s infrastructure.
The Dama net shell
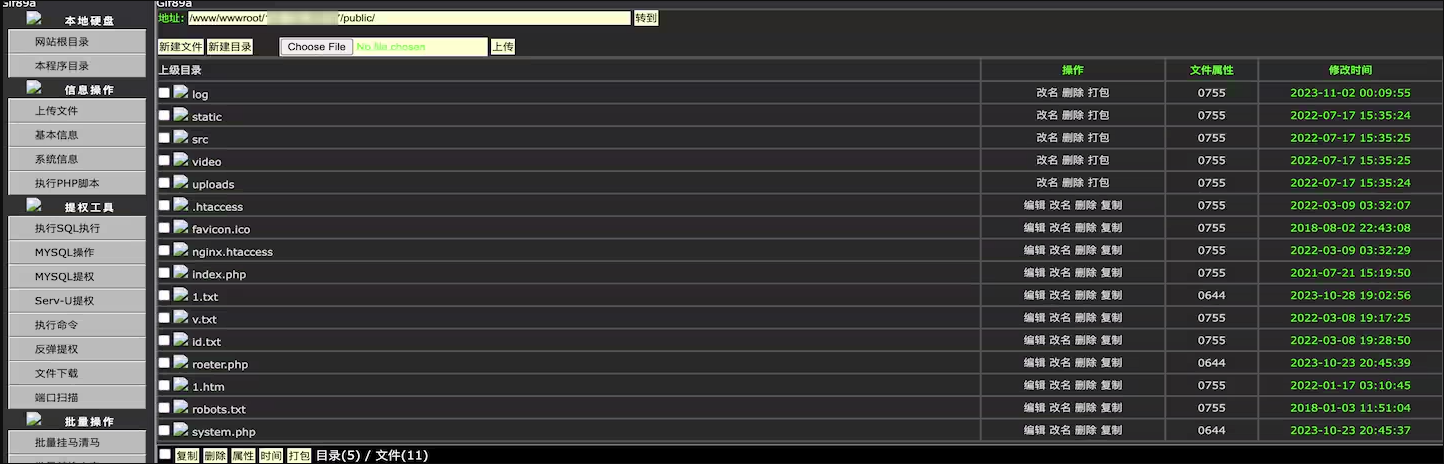
Dama has superior capabilities enabling the menace actors to navigate the file system on the compromised server, add recordsdata, and collect system information, primarily aiding in privilege escalation.
It might additionally carry out community port scanning, entry databases, and bypass disabled PHP features for shell command execution.
Supply: Akamai
A notable omission from Dama’s capabilities is the dearth of a command-line interface, which might enable menace actors a extra hands-on strategy to executing instructions.
Akamai notes that this lacking performance is notable given Dama’s in any other case intensive performance.
Mitigation
Exploiting 6-year-old flaws serves as one other reminder of the persistent downside of poor vulnerability administration, as attackers, on this case, leverage safety vulnerabilities patched a very long time in the past.
The really helpful motion for probably impacted organizations is to maneuver to the latest ThinkPHP, model 8.0, which is protected towards recognized distant code execution bugs.
Akamai additionally notes that the focusing on scope of this marketing campaign is broad, even impacting methods not utilizing ThinkPHP, which suggests opportunistic motives.